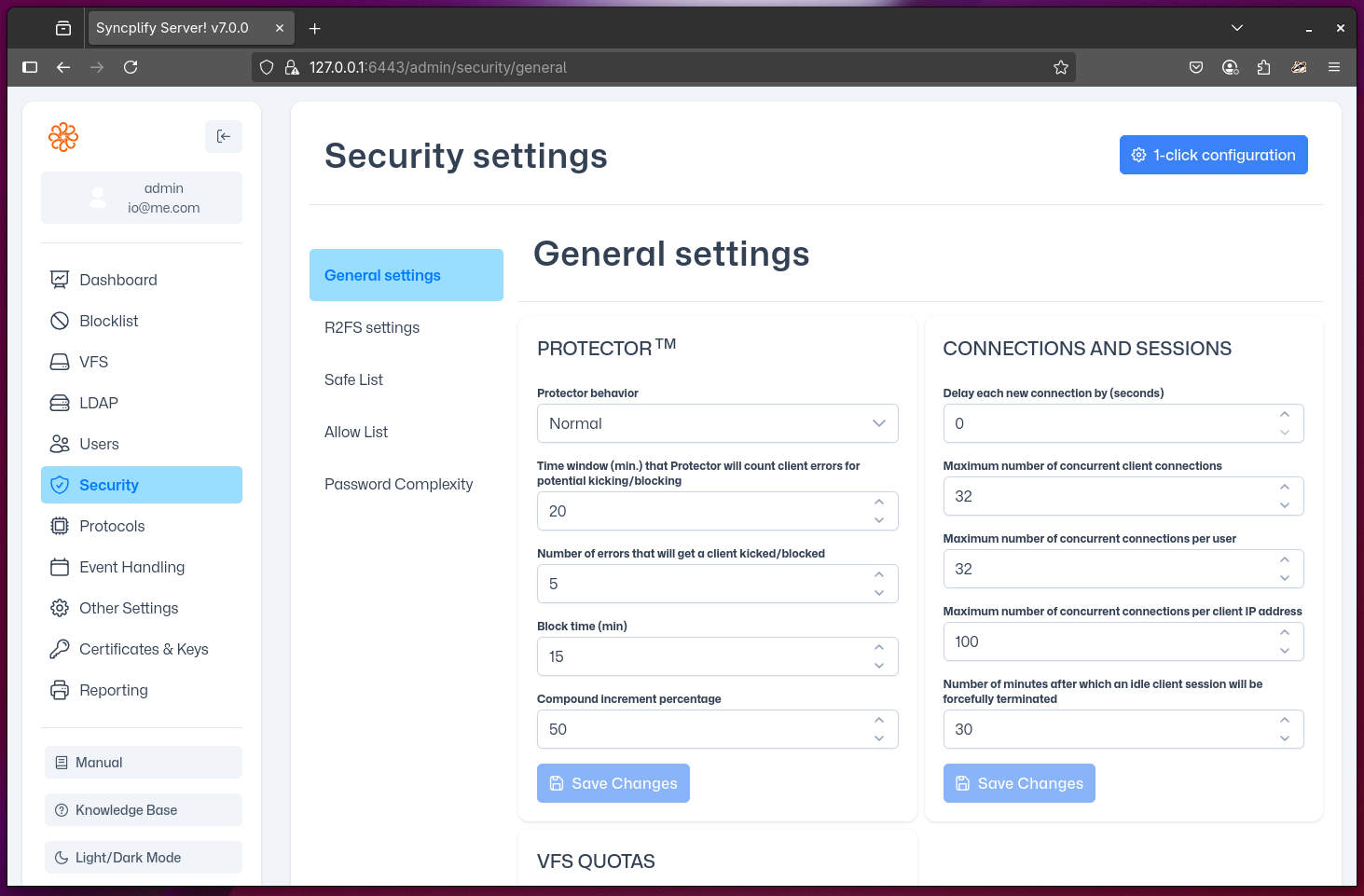
General security settings
This sections allows you to configure several general security settings for your Syncplify Server!, grouped into 3 main categories:
- Protector™: allows you to configure various aspects regarding how the Protector™ subsystem operates, together with its automatic block-listing capabilities (read more below)
- Connections and sessions: allows you to define certain settings and limits regarding how your Server! handles incoming client connections and sessions
- VFS Quotas: allows you to configure the interval between refresh operations to verify (and, if needed, auto-update) the quotas of your virtual file systems (VFS)
Protector Behavior Levels
Protector behavior defines how strictly the server validates client commands, payloads, and protocol correctness. Depending on the selected level, non-compliant behavior may be ignored, rejected, or recorded as a strike (i.e. counted toward block-listing).
Permissive: Tolerant mode. The server accepts and responds to unknown/unrecognized commands or payloads by returning a generic error response, without recording a strike. Security-relevant events are still recorded as strikes, including (but not limited to): unexpected connection resets, authentication failures, buffer overflow/underflow attempts, and negotiation of disabled or non-existent encryption/MAC/KEx algorithms.
Normal: Default mode. Same as Permissive, except unknown/unrecognized commands and payloads are recorded as strikes. This is the recommended behavior level for most Syncplify Server! deployments, it provides a very strong level of protection without interfering too much with day-to-day operation.
Strict: Validation mode. Same as Normal, and additionally validates command targets. Commands that reference invalid or non-existent resources are recorded as strikes (for example, issuing the FTP
SIZEcommand against a file that does not exist).Paranoid: Zero-tolerance mode. Requires full protocol correctness at all times. Any deviation in commands, payload formatting, sequencing, or state transitions is rejected and recorded as a strike. This level is intended only for controlled environments where the client implementation is known and guaranteed to be fully compliant.
